Big Cyber Loopholes that Retail Businesses Hope They Know Sooner
As a consumer, technology drives and brings convenience to our lives and the retail business is also one of the most benefit-earned sectors from technology. Companies to implement technology into the system to enhance their productivity, manage resources, deliver a smooth customer experience and most of all, profits.
However, the more advanced the technology, the more likely that businesses are exposed to the potential cyber attack. No matter the business size, large or small, the consequences that these cyber attack can be catastrophic to business operation and it would be an understatement not to mention, customer privacy. You have probably remembered Facebook’s scandal for not protecting user’s information adequately and let it slip right through its finger.
Another notorious example is the Wanna Cry ransomware hacking to million of computers around the world in various industries. Retail businesses nowadays are integrating technology into their business like every other industry by storing customer data ranging from name, age, address and their shopping pattern of thousand or even million of customers. Its purpose is to deliver the best customer experience with the business’s product and services – check out 7 practical benefits of personalization.
However, the thought of protecting from a cyber attack as companies are expanding in the digital world is not their top-of-mind priority. Identity theft and phishing for various personal and organizations’ uses may occur if retail businesses do not make their move. This article is not going to discuss the threats of a cyber attack in detail because we are all fully aware of how devastating those events have been. Instead, the article provides you a heads up of what kind of loopholes there are that may drive your business to become vulnerable for a cyber attack.
Customer Data
For a consumer business, the pool of data that the companies own can be the most vulnerable spot for a cyber attack. Why? Companies are leveraging their competitive advantage by utilizing data into their decision-making process.
Data is one of the most critical elements for every business, and such heavy dependence on data makes companies exposed to cyber attack more easily. Companies store hundred to thousands of customer data in their system. The information varies from the customer’s name, address, phone number, email, etc.
Moreover, sensitive information such as bank account’s number, financial balance, credit card number may cause tremendous financial risk for so many customers. Right now, more and more people are well aware of the data they are giving to the companies.
It’s companies’ job to provide assurance and show that they are taking appropriate steps to mitigate cyber thieves from benefiting customers information. Utilizing data to deliver happier customer experience shall make a positive impact on future purchase. We want to avoid the PR crisis like Facebook and Cambridge Analytica, don’t we all?
Companies’ Personnel
Another loophole that retail companies should take into consideration is from within its system. It is the personnel. Human resources can be the most fragile layers over the cyber attack. Especially, the not-so-much experience with computer and technology. These employees do not have any harmful intention toward the organization, but their lack of ability to understand which site to click or which email not to answer can pull cyber threat to the organization.
Therefore, to mitigate cyber risk, it is critical to attract, train, retain top tech talent to manage the system better. In the meantime, hosting educational programs for the employee to take the matter of cyber risk seriously deserve a spot on the c-level executives’ to-do list.
Speaking of c-level executives, how would the organization be prepared if the board of directors doesn’t have or haven’t had the mindset to prevent a cyber attack actively?
People usually turn their finger and questions towards those who are in charge, and it’s not the best scenario when the board of director doesn’t have the proper protocol for a cyber attack. Poor management mindset may not be the most apparent loophole, but it should be the most critical one for the organization.
Retail business and other businesses in various industries should consider gaining a deep insight into the cyber landscape. Because investing in advanced technology to manage efficiently doesn’t mean that the matter of cyber risk should be taken so lightly.
Connected Products and Devices
One more internal factor that can pull a threat to cyber risk is the connection of devices. IoT – Internet of Things is probably the noblest integration of the 4.0 industrial revolution achievements.
The benefits are countless.
You can easily input information on one device, and that information will be shared and synchronized with other devices. Such synchronization brings convenience to the user and hence, improve workflow productivity.
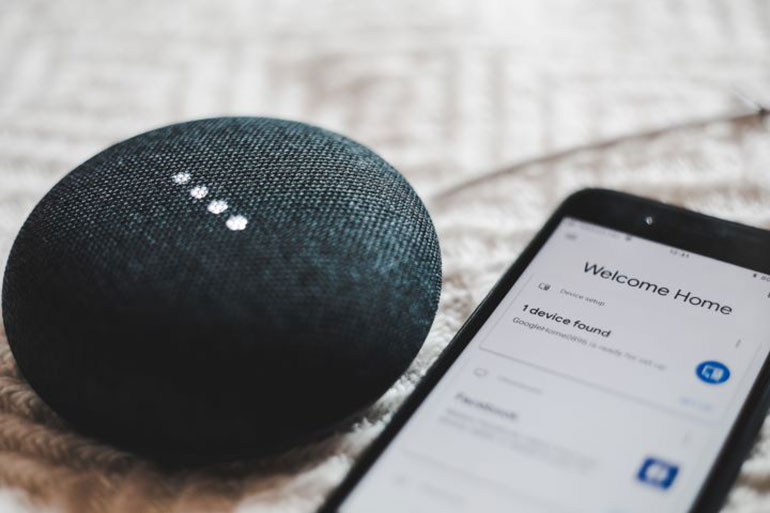
However, the loophole that cybercriminal can sneak into the system is the poor protecting system or weak firewall. Hackers can control sensors which are attached to your devices and hijack information from those devices.
And if your devices are connected to other devices, the whole network will be affected which resulting in the network shutdown. Such a scenario is much more devastated and more catastrophic. It is essential that consumer businesses ensure the security of connected products if both companies and consumers are to exploit the advantages from it.
What Are the Solutions to Deal with the Cyber Matter?
Besides some of the answers that I have mentioned above, there are a few more options that businesses should take into consideration:
Pull a Full Security Workup from Head to Toe:
Running a full scan helps you to determine where and which part of your system underperforms. The effort also helps the board to determine whether the current system
Filter User Data:
Keep Track of the Vendor Sites:
Using third-party plugins or modules into your system could be an economical approach for most businesses. Integrating those software means that your company reduce the number of staffs managing those complicated software but in fact, you open more doors for more individuals to have the chance to affect the application’s security.
The Envzone Solution:
We deliver you a holistic approach to your business’s challenge, and we protect your business along the way with our fantastic software team based in Vietnam
Sources: Deloitte and Forbes
You Might Also Like: